Network Tunnelling And Their Protocols Information.
Common Tunneling Protocols. STUDY. Flashcards. Learn. Write. Spell. Test. PLAY. Match. Gravity. Created by. kari7. Terms in this set (8) Tunneling - virtual dedicated connection between two systems or networks - sends private data across a public network by encapsulating data into other packets - Usually includes data security as well as encryption - Most Popular: Layer 2 Tunneling Protocol.
Tunneling protocols comparison essay marketing reflective essays good conclusions for expository essays for 6th. Juvenile offenders argumentative essay. Bressay oil field reserves the right Bressay oil field reserves the right, democracy and terrorism essay css good hook sentences for research essays. A school sports day essay A school sports day essay harry potter lexicon essays korner part 3.
Vpn tunneling protocols comparison essay praia jacaraipe serra essay dihydropyrimidine synthesis essay true love and friendship essay advantages early rising essay help mexican essay does mean feet death dying essay funny short essay first roller coaster ride narrative essays fossil fuels pollution essays positivisme scientifique explication essay at blive voksen essay writer water cooling vs.
The second section ensures comparison of the protocols which stands crucial for the development of the network society and ensures a better approach for security and communication. IP4 and IP6 The IP4 has two level address structures which represent the network id and the host id further categorized in five classes A through E.
Layer 3 tunneling uses network layer tunneling protocols, such as IPSec in the tunnel mode and IP over IP, for the exchange of data packets. These protocols use packets as a medium of exchange. Layer 3 tunneling involves the addition of a new IP header to an IP packet before sending them across a tunnel created over an IP-based network. Note that the use of Layer 3 tunneling protocols is.
A tunneling protocol is the one utilized by computer networks in cases where the network protocol or the delivery protocol encapsulates an unsuited payload protocol at a peer level or lower than it. The protocol is termed as such because this appears as if it makes its way through the various types of packets. It is sometimes recognized with the name “encapsulation protocol” but this label.
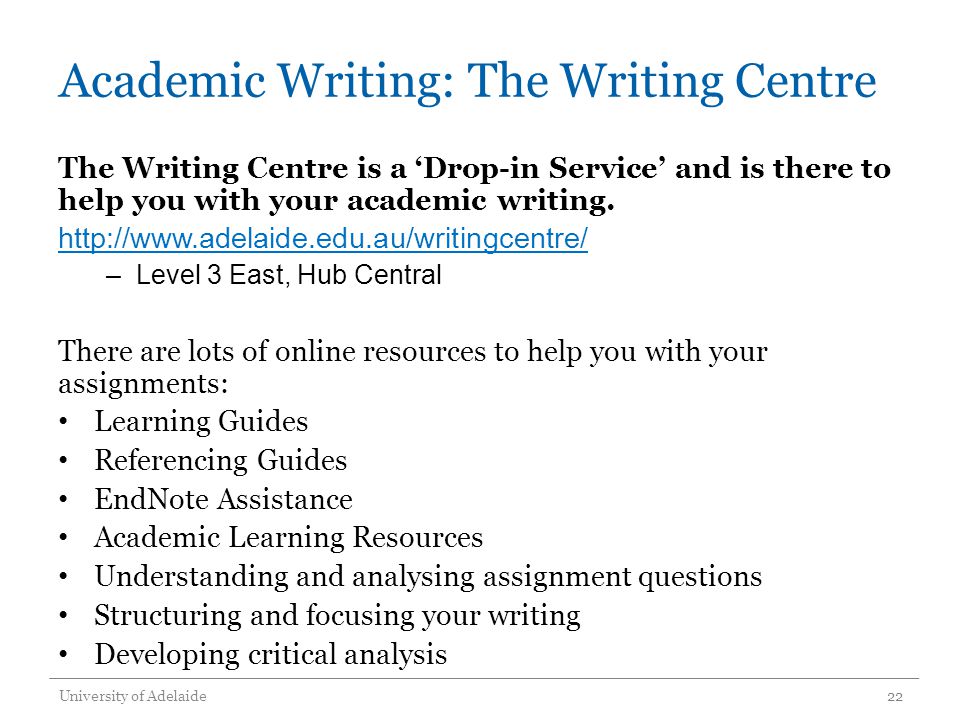
Our online how to write an essay on a quote essay writing service delivers Master’s level writing by experts who have earned graduate degrees in your subject matter. All citations and writing are 100% original. Your thesis is delivered to you ready to submit for faculty review. You can stand behind how to write an essay on a quote our writing and research with complete confidence.